Archive for March 2026
March Tech Bytes Newsletter
March Tech Bytes: Strengthening Security and Smart IT for 2026This month’s edition focuses on practical strategies to improve security, reduce risk, and build resilient operations. Inside, we cover preparing for Agentic AI, securing third‑party access, avoiding cloud‑only pitfalls, strengthening MFA, and protecting your business from emerging cyber threats. Read More!
Read MoreZero-Trust for Small Business: No Longer Just for Tech Giants
The Zero Trust security model operates on this simple mantra: “Never trust, always verify.” It assumes threats exist both outside and inside your network, requiring strict identity verification for every person and device trying to access resources. For small businesses, this is no longer an enterprise-only concept, and adopting a Zero Trust architecture is now…
Read MoreManaging Cloud Waste as You Scale
Unchecked cloud resource management transforms the cloud’s promise of agility into a source of bloated and unpredictable spending known as “cloud waste” that eats into your bottom line. As such, business leaders need to adopt strategies that treat cloud spend as a business variable that requires continuous cost optimization to identify and eliminate waste. The…
Read MoreThe “Insider Threat” You Overlooked: Proper Employee Offboarding
A lax employee offboarding checklist is a critical security gap. When a team member leaves, their digital access does not automatically disappear. Neglecting a formal IT offboarding process can lead to data theft, sabotage, and compliance nightmares. Proactive offboarding is not administrative busywork; it is a vital layer of cybersecurity for employees that protects your…
Read MoreBeyond Chatbots: Preparing Your Small Business for “Agentic AI” in 2026
As AI solutions continue to advance, the landscape is also shifting from basic chatbots into more specialized “Agentic AI” systems that execute multistep tasks autonomously. For small businesses, this shift promises increased efficiencies but also creates new security and operational complexities. Success with AI agents will depend on a foundation of clean data and clear…
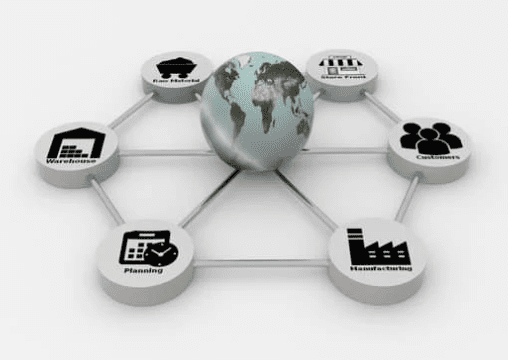
Read MoreThe Supply Chain Trap: Why Your Vendors Are Your Biggest Security Risk
Your cybersecurity is only as strong as your weakest vendor’s defenses. Modern third-party cyber risk is a massive threat, as attackers target smaller vendors to reach larger clients. As such, a vendor security assessment is no longer optional, and businesses must move beyond trust alone and actively manage supply chain vulnerabilities through continuous monitoring and…
Read More